Find out how hackers and fraudsters typically target organization with business-email compromise campaigns that are just too realistic.
Business Email Compromise (BEC) email attacks against businesses in air transportation, industry, retail, IT, and delivery are on the rise, according to data from Kaspersky’s customer ecosystem.
Hackers expend substantial time and resources to launch such targeted attacks, and just one successful campaign may lead to a big payoff worth many millions.
In a BEC attack, hackers usually initiate an email exchange with a company employee in order to gain their trust and encourage them to take actions unknowingly to help the attackers. The typical way is to use a hijacked employee’s email account or an account that spoofs specific employees’ email addresses to contact potential victim employees.
Sometimes, cybercriminals steal the credentials of an employee to target their higher-ranking colleagues. In most cases, hackers aim for a company’s money, although there have been isolated incidents bent on seeking confidential information (e.g. a customer database or sensitive business developments information).
Top three BEC schemes
Here are the most popular BEC schemesthatKaspersky experts have encountered:
- CEO fraud
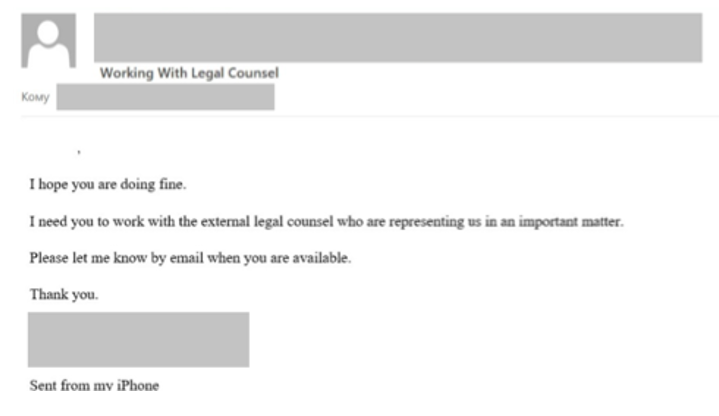
In such a scenario, an employee will receive a fake email from a senior management colleague. Attackers may use this persona to convince the employee to share information with a ‘legal counsel’ or similar party (which is either a dummy or compromised account) and will try to steal confidential company data or information to use in further attacks at the organization.
- Fake payroll change request
In this case, the accounting department may receive a message from an (alleged) employee asking to change their salary payment credentials. If the accountant replaces the card details in the payroll system, the salary intended for the employee will go to the attacker.
- Fake invoices
This letter will come to the accounting department, but in this case, it appears to come from a supplier or third party regarding a delay in the payment of an invoice. Again, if the accountant succumbs to this trick, the money will go to the cybercriminals.
To avoid falling victim to BEC attacks, organizations should observe these best practises:
- Use reliable security solutions with advanced anti-phishing and anti-spam technologies.
- Improve staff digital literacy and cybersecurity awareness. Especially important are awareness of social engineering techniques.
- Train staff to observe non-disclosure rules about corporate information or even personal information when accessing systems with open access, for example, cloud services.
Said the firm’s Head of Content Filtering Methods Research, Alexey Marchenko: “To execute BEC attacks, cybercriminals always carefully harvest data about their victim and then use it to build trust. Some of these attacks are possible because cybercriminals can easily find names and job positions of employees, their exact locations, dates of holidays, lists of contacts and more in open access. Fraudsters generally use a wide range of techniques and methods of social engineering to gain a victim’s confidence and commit malicious operations, so users need to be extra careful at work.”

















