A recent report uncovered this and surges in phishing and Emotet malware activities and as rising threats last year.
Waterhole attacks (a strategic website compromise attack) and phishing have been identified as the top threat vectors in 2019, accounting for 84% of all cyberattacks detected in Singapore, according to Ensign Infosecurity’s Singapore Threat Landscape 2019 report.
The report also revealed that the high technology industry (including cloud, data center and web hosting service providers) in Singapore was the top target for threat actors in 2019. Companies in this sector were attractive targets as threat actors often exploit such infrastructure to expand their botnet activities as well as target other organizations whose servers are being hosted therein.
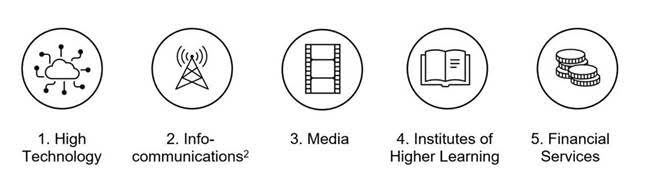
For last year, the top five most targeted sectors in Singapore were:
Said Lee Shih Yen, Senior Vice President, Ensign Labs, Ensign InfoSecurity: “Relevance and context are the most important elements when analyzing cyber threat intelligence, as threats and trends can differ across geographies, sectors and companies. Only by combining different global and local cyber threat intelligence sources are we able to derive accurate and deep information about Singapore-specific threats and help organizations bolster their cybersecurity posture by providing contextualized, actionable insights.”
Top two threat vectors
Waterhole attacks were the most prevalent threat vector of 2019, contributing to nearly half (47%) of all detected cyberattacks in Singapore. Waterhole attacks occur when an attacker compromises a website and replaces its content with malicious payloads. Unsuspecting victims who then download content from these websites will infect their machines with malware.
This method enables threat actors to execute supply chain attacks where they infect servers containing updates of popular software and replace these updates with malicious codes to spread malware. This allows threat actors to achieve mass infection, especially when the vulnerable web server is popular and trusted by end users.
The other top threat vector in Singapore is phishing (also known as malspam), and almost two out of five (37%) of the detected cyberattacks in 2019 were attributed to it. Phishing is an effective social engineering technique and a popular tactic for threat actors as it is easy to execute and able to target a wide pool of victims.
Top threat actor in SG
Both waterhole attacks and phishing are the favoured techniques of the threat actor group, APT32 (also known as Oceanlotus) and the increase in its activities is higher than that of all other threat actor groups in Singapore last year.
APT32, which has been active since 2014, concentrates its activities in Southeast Asia and has targeted multiple private sectors and governments across the region. In 2019, APT32 was linked to 23 out of 34 sectors (68%) in Singapore. The spread of cyberattacks across diverse sectors aligns with APT32’s strategy of running opportunistic phishing email campaigns throughout the year.
The report stated that from April to May 2019, a 500% spike was detected in APT32 activities in Singapore’s manufacturing sector. From October to December 2019, an 800% increase in APT32 activities was likely the result of seasonal phishing campaigns that this group was running during the shopping and festival seasons.
Emotet a rising threat
The report also found that Emotet was the most prominent malware in Singapore last year. Ensign had detected Emotet activities in 27 out of 34 (79%) sectors in 2019, impacting more than 1,200 companies. The widespread attacks across a broad spectrum of sectors indicate the attacks were likely opportunistic and executed in the form of spam campaigns.
In the first half of 2019, especially from February to April, high volumes of probing activities on port 445 were detected, which is a vulnerable port targeted by Emotet. It is likely that threat actors were scanning for vulnerable targets as part of their reconnaissance.
In Q4 of 2019 (1 October to 31 December), Emotet phishing detections spiked by nine times compared to that in the previous quarter. This can be attributed to the launch of phishing email campaigns by various threat actor groups. In the same period, there was an 11-fold increase in outgoing Emotet C2 (command and control) detections compared to Q3 of 2019. The increase in outgoing traffic with Emotet Indicators-of-Compromise (IoCs) can be attributed to servers being infected by phishing spam campaigns.
“As modular, polymorphic malware such as Emotet are emerging faster than ever, conventional and reactionary signature-based threat detection is inadequate in today’s cyber threat landscape. Organizations need to have a proactive cybersecurity posture, and this not only requires access to hyper-localized, actionable threat intelligence, but also behavior-based security capabilities that can detect changes in adversary tactics and techniques based on the MITRE ATT&CK framework,” added Shih Yen.

















