This includes over 70% of 365 ICS flaws published in the National Vulnerability Database for the first half of 2020.
More than 70% of industrial control system (ICS) vulnerabilities can be exploited remotely, highlighting the importance of protecting internet-facing ICS devices and remote access connections.
This is according to a report released by a specialist in operational technology security, Claroty, comprising an assessment of 365 ICS vulnerabilities published by the National Vulnerability Database (NVD) and 139 ICS advisories issued by the Industrial Control Systems Cyber Emergency Response Team (ICS-CERT) during 1H 2020, affecting 53 vendors. Out of this data set, the Claroty Research Team had discovered 26 of the vulnerabilities.
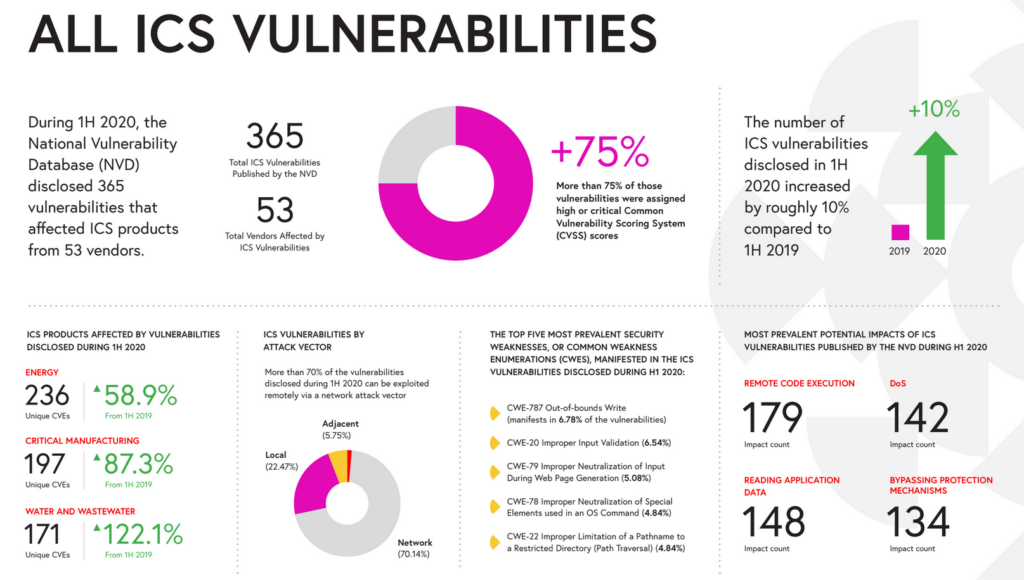
Compared to 1H 2019, ICS vulnerabilities published by the NVD have increased by 10.3% from 331, while ICS-CERT advisories have increased by 32.4% from 105. More than 75% of vulnerabilities were assigned high or critical Common Vulnerability Scoring System (CVSS) scores.
Said Amir Preminger, VP of Research, Claroty: “There is a heightened awareness of the risks posed by ICS vulnerabilities and a sharpened focus among researchers and vendors to identify and remediate these vulnerabilities as effectively and efficiently as possible. We recognized the critical need to understand, evaluate, and report on the comprehensive ICS risk and vulnerabilities landscape to benefit the entire OT security community. Our findings show how important it is for organizations to protect remote access connections and internet-facing ICS devices, and to protect against phishing, spam, and ransomware, in order to minimize and mitigate the potential impacts of these threats.”
Prominence of RCE vulnerabilities
According to the report, more than 70% of the vulnerabilities published by the NVD can be exploited remotely, reinforcing the fact that fully air-gapped ICS networks that are isolated from cyber threats and vulnerabilities have become vastly uncommon.
Additionally, the most common potential impact was remote code execution (RCE), possible with 49% of vulnerabilities—reflecting its prominence as the leading area of focus within the OT security research community, followed by the ability to read application data (41%), cause Denial-of-Service (DoS) (39%), and bypass protection mechanisms (37%).
The prominence of remote exploitation has been exacerbated by the rapid global shift to a remote workforce and the increased reliance on remote access to ICS networks in response to the COVID-19 pandemic.
Vulnerabilities in certain sectors on the rise
The report shows that the energy, critical manufacturing, and water & wastewater infrastructure sectors were by far the most impacted by vulnerabilities published in ICS-CERT advisories during 1H 2020.
Of the 385 unique Common Vulnerabilities and Exposures (CVEs) included in the advisories, energy had 236, critical manufacturing had 197, and water & wastewater had 171. Compared to 1H 2019, water & wastewater experienced the largest increase of CVEs (122.1%), while those in critical manufacturing have increased by 87.3%, and energy by 58.9%.
The team from Claroty were responsible for 26 ICS vulnerabilities disclosed during 1H 2020, prioritizing critical or high-risk vulnerabilities that could affect the availability, reliability, and safety of industrial operations. The team focused on ICS vendors and products with vast install bases, integral roles in industrial operations, and those that utilize protocols in which Claroty researchers have considerable expertise. These 26 vulnerabilities could have serious impacts on affected OT networks, because more than 60% enable some form of RCE.
For many of the vendors affected by Claroty’s discoveries, this was their first reported vulnerability. As a result, they proceeded to create dedicated security teams and processes to address the rising vulnerability detections due to the convergence of IT and OT.