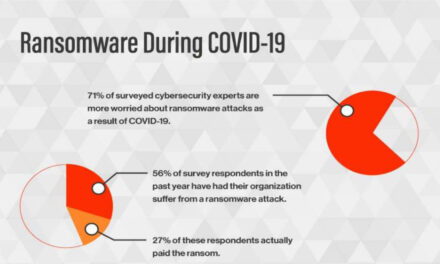
Global survey shows the average cost of recovery is US$1.4 million if organizations pay the ransom, otherwise it is US$730,000.
Paying cybercriminals to restore data encrypted during a ransomware attack is not an easy and inexpensive path to recovery. In fact, the total cost of recovery almost doubles when organizations pay a ransom.
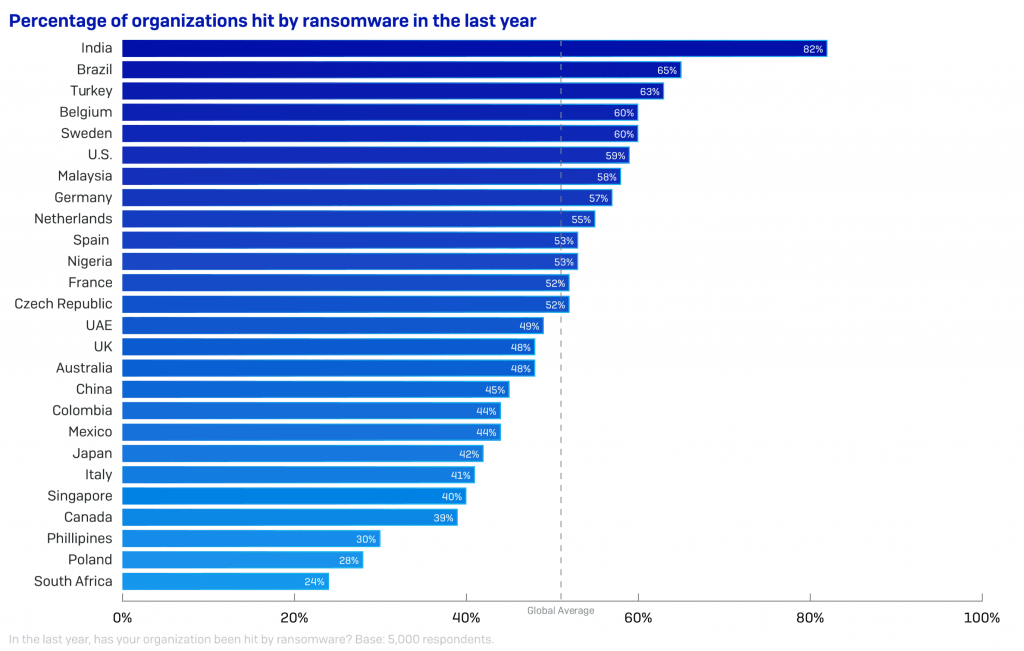
This is the finding of a survey by Sophos which polled 5,000 IT corporate decision makers in 26 countries across six continents, including Europe, the Americas, Asia-Pacific and central Asia, the Middle East, and Africa.
Additionally, the report states that almost half (40%) of organizations in Singapore had experienced a ransomware attack in the previous 12 months. Data was encrypted in 63% of attacks that successfully breached an organization.
Also, the average global cost of addressing the impact of such an attack, including business downtime, lost orders, operational costs and more, but not including the ransom, was US$730,000. This average cost rose to US$1.4 million, almost twice as much, when organizations paid the ransom.
In Singapore, more than one quarter (28%) of organizations hit by ransomware in Singapore admitted getting their data back by paying the ransom.
Said Chester Wisniewski, principal research scientist, Sophos: “Organizations may feel intense pressure to pay the ransom to avoid damaging downtime. On the face of it, paying the ransom appears to be an effective way of getting data restored, but this is illusory. Sophos’ findings show that paying the ransom makes little difference to the recovery burden in terms of time and cost. This could be because it is unlikely that a single magical decryption key is all that’s needed to recover. Often, the attackers may share several keys and using them to restore data may be a complex and time-consuming affair.”
More than half (54%) of the IT managers surveyed in Singapore were able to recover their data from backups without paying the ransom. In a very small minority of cases (2%), paying the ransom did not lead to the recovery of data. At a global level, for 5% of public sector organizations, paying the ransom did not lead to the recovery of data. In fact, 13% of the public sector organizations surveyed never managed to restore their encrypted data, compared to 6 % of organizations globally.
However, contrary to popular belief, the public sector was least affected by ransomware globally, with just 45% of the organizations surveyed in this category saying they were hit by a significant attack in the previous year. At a global level, media, leisure and entertainment businesses in the private sector were most affected by ransomware, with 60% of respondents reporting attacks.
Attackers increase pressure to pay
SophosLabs researchers have also published a new report on Maze Ransomware, which looks at the tools, techniques and procedures used by this advanced threat that combines data encryption with information theft and the threat of exposure. This approach, which Sophos researchers have also observed being adopted by other ransomware families, like LockBit, is designed to increase pressure on the victim to pay the ransom.
The report will help security professionals understand and anticipate the evolving behavior of ransomware attackers and develop ways to protect their organizations.“An effective backup system that enables organizations to restore encrypted data without paying the attackers is business critical, but there are other important elements to consider if a company is to be truly resilient to ransomware,” added Wisniewski.
“Advanced adversaries like the operators behind the Maze ransomware don’t just encrypt files, they steal data for possible exposure or extortion purposes. We’ve recently reported on LockBit using this tactic. Some attackers also attempt to delete or otherwise sabotage backups to make it harder for victims to recover data and increase pressure on them to pay. The way to address these malicious manoeuvres is to keep backups offline, and use effective, multi-layered security solutions that detect and block attacks at different stages.”