Lax or risky IAM configurations can lead to multi-million dollar losses, and regional trends show worrying signs.
In its recent Cloud Threat Report for H2 2020, Palo Alto Networks’ threat intelligence team Unit 42 has revealed key risks to global enterprises adopting cloud workloads.
Identity and access management (IAM) misconfigurations are prevalent across cloud accounts and represent a significant security risk to organizations. In the Asia Pacific region and Japan (JAPAC) in particular, enterprises displayed poor cloud identity hygiene that could potentially expose them to attacks like crypto jacking, ransomware and the theft of intellectual property.
Also, 75% of JAPAC organizations (74% in the EMEA region) were found to be using Google Cloud VM instances with administrative rights, providing an easy path for cyber criminals to use their cloud resources to perform attacks.
During a Red Team exercise, for example, researchers were able to discover and leverage IAM misconfigurations to obtain admin access to a customer’s entire Amazon Web Services (AWS) cloud environment—a potentially multi-million-dollar data breach in the real-world.
Other key findings:
- 60% of JAPAC organizations were more likely to allow ‘non-corporate’, third party accounts such as managed security service provider (MSSP) accounts or personal accounts, to have access to their Google Cloud environments compared to organizations in Americas (49%).
- 82% of JAPAC organizations were more likely to have AWS user accounts inactive for more than 30 days.
- 57% of JAPAC organizations did not enable multi-factor authentication within their AWS environments for IAM user accounts.
- 27% of IAM root accounts in JAPAC did not enable multi-factor authentication functionality, even with the option to do so.
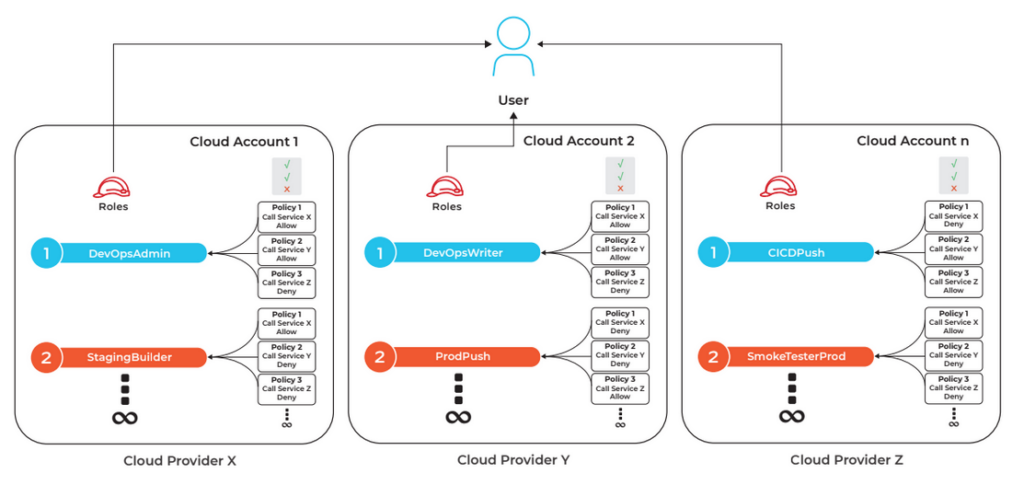
According it the firm’s Public Cloud CSO Matthew Chiodi: “…Understanding effective permissions and identifying risky policies across hundreds of roles and different cloud service providers are tasks best left to algorithms and automation.”
The report recommends three ways to stay secure in the Cloud: maintain situational awareness of the latest adversary tactics regarding targeting IAM roles and policies; empower DevOps and security teams to stay ahead of the threat curve for protecting their cloud environments; and instilling a security-first mindset that hardens IAM roles and policies.