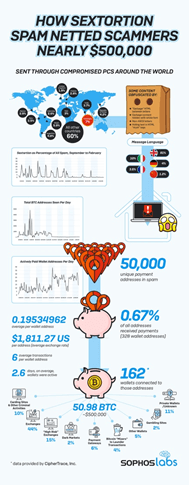
Global botnets installed on compromised devices in these places were instrumental in the dissemination of sextortion spam.
What actually happens to the ransom money hauled from victims by cybercriminals?
Researchers sniffed out the answer after tracing the origin of millions of sextortion spam emails launched between September 2019 and February 2020 and then analyzed what happened to the money deposited by victims in attackers’ bitcoin wallets.
The bitcoin value extorted from the scams totalled approximately US$500,000. Researchers from SophosLabs believes their investigative report is the first to trace a bitcoin haul from sextortion.
Sextortion is a widely-used form of spam attack that accuses the recipient of visiting a pornographic website and threatens to share video evidence with the recipient’s friends and family unless ransom is paid. In the examples analyzed, recipients were asked to pay up to US$800 worth in bitcoin into designated wallet addresses.
The researchers worked with cryptocurrency forensics specialist CipherTrace to track the flow of the money from victims’ wallets. The study found that the extorted funds were used to support subsequent illicit activity, such as transacting with dark web marketplaces and buying stolen credit card data. Other funds were quickly moved through a series of wallet addresses to be consolidated, put through “mixers” in an attempt to launder the transactions or converted to cash.
Said Tamás Kocsír, SophosLabs lead security researcher for this study: “The cybercriminal underworld is an intricate web and SophosLabs’ research shows how attackers used the money raised in one operation to invest in another. Sextortion scams prey on fear and this makes them an effective way of making quick money.”
Across the five months of the investigation, Kocsír’s team saw wave after wave of attacks, often taking place over the weekend and sometimes accounting for up to a fifth of all spam tracked at SophosLabs. While most recipients either did not open the email or did not pay, “enough of them did to net the attackers around 50.9 bitcoin, equivalent to nearly US$500,000.”
The scammers exploited global botnets installed on compromised devices to dispatch millions of spam emails to recipients around the world. The top 10 countries originating such spam are Argentina, Brazil, Colombia, India, Italy, the Republic of Korea, Mexico, Peru, Poland and Vietnam. The spam messages were in English (81%), Italian (10%), German (4%), French (3.5%) and Chinese (1.2%).
“Spam campaigns are relatively cheap and easy to implement, but the assumption that this means they are launched only by low-skilled, opportunistic attackers could be inaccurate,” said Kocsír. “Our research found that some of the scam emails featured innovative obfuscation techniques designed to bypass anti-spam filters. Examples of this include breaking up the words with invisible random strings, inserting blocks of white garbage text, or adding words in the Cyrillic alphabet to confuse machine scanning.”
These are not beginner techniques, and they are a good reminder that spam attacks of any kind should be taken seriously. “A robust approach to cybersecurity is essential. If you are worried about becoming the target of a sextortion scam, disable or cover the camera on your computer,” advised Kocsír.