The impact of APAC’s AI buildout on cybersecurity in 2026
By Victor Ng | Dec 9, 2025
Is your AI secretly sabotaging your organization?
By Victor Ng | Dec 1, 2025
Lessons learnt from the first reported AI-orchestrated attac...
By Victor Ng | Nov 28, 2025
The new face of fraud in the AI era
By Victor Ng | Nov 25, 2025
Shadow AI – the hidden risk in APAC organizations
By Victor Ng | Nov 24, 2025
HOT TOPIC CENTER
SECURITY NEWS
Urgent patches for multiple critical vulnerabilities in iOS/iPadOS released
By CybersecAsia editors | Dec 16, 2025
Updates tackle more than 30 risks across components such as the kernel, App Store, and apps such as Messages and Photos.
-

AI video tool fuels disinformation surge
By CybersecAsia editors | Dec 15, 2025
-

-

Just when we thought AI-powered IDEs were invaluable…
By CybersecAsia editors | Dec 12, 2025
EXPERT OPINIONS
Unified Zero Trust is vital to plug IAM gaps and exploitable risks
By Apu Pavithran, founder and CEO, Hexnode | Oct 14, 2025
Fragmented identity and access management tools and processes increase risk. Continuous, proof-driven security is the key to foiling attackers.
-

-

Google tightens Android sideloading
By CybersecAsia editors | Sep 2, 2025
-

Experts weigh in on Singapore’s response to UNC3886
By CybersecAsia editors | Aug 8, 2025
TIPS
Every video in social media is now suspect: Stay vigilant to deepfakes!
By L L Seow | Dec 16, 2025
Malicious actors regularly bypass generative-AI safeguards to flood social media platforms with realistic fakes content. Time to stop spreading their lies!
-

-

-

Cybersecurity predictions for 2026 start here
By Various contributors, Exabeam | Dec 11, 2025
Are Your Business Secrets Really Secret and Secure?
Jan 21, 2025
“Bump in the night”: What’s next?
Sep 26, 2024
INFOGRAPHICS

Verizon 2025 Mobile Security Index Report Infographic


Phishing trends in Q3 2024 Infographic

Sumsub’s First Global Fraud Index Infographic

Verizon 2024 Mobile Security Index Infographic

Acronis Cyberthreats Report H1 2024 Infographic
Latest
Cloud SecurityHOSTWAY gains 73% operational efficiency for private cloud operations
By CybersecAsia editors | Oct 2, 2025
With NetApp storage solutions, the Korean managed cloud service provider offers a lean, intelligent architecture, powered by automation and an Infrastructure-as-Code approach.
-

-

Before we take the plunge into the AI-powered metaverse…
By Victor Ng | Nov 12, 2024
-

Latest
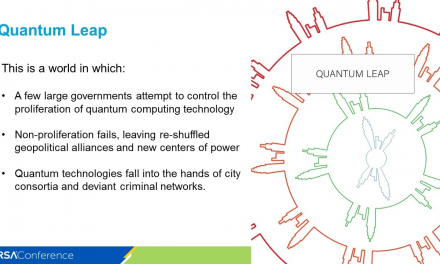
Cyber WarfareIs the world ready to be united against intensifying 2025 cyber warfare?
By Nadir Izrael, CTO, Armis | Nov 19, 2024
From AI-emboldened organized cybercriminals to state-sponsored quantum threats, the cyber landscape could run out of control unless we act now
-

-

Ransomware still the #1 cyber threat: report
By CybersecAsia editors | Jan 30, 2023
-

Latest
Cyber IntelligenceW3LL-oiled machine: report uncovers covert BEC phishing empire targeting Microsoft 365
By CybersecAsia editors and webmaster webmaster | Sep 7, 2023
A new threat report “W3LL DONE: HIDDEN PHISHING ECOSYSTEM DRIVING BEC ATTACKS” has detailed the operations of W3LL, a threat actor behind a phishing empire that has remained largely unknown until now.
-

-

-

Making cyber-resilience part of your organization’s balance sheet
By Victor Ng | Apr 26, 2022
Voters-draw/RCA-Sponsors
CybersecAsia Voting Placement
Gamification listing or Participate Now
|
PARTICIPATE NOW |
|
|
Vote Now -Placement(Google Ads)
Top-Sidebar-banner
Whitepapers

Closing the Gap in Email Security:How To Stop The 7 Most SinisterAI-Powered Phishing Threats
Insider threats continue to be a major cybersecurity risk in 2024. Explore more insights on …Download Whitepaper
2024 Insider Threat Report: Trends, Challenges, and Solutions
Insider threats continue to be a major cybersecurity risk in 2024. Explore more insights on …Download Whitepaper
AI-Powered Cyber Ops: Redefining Cloud Security for 2025
The future of cybersecurity is a perfect storm: AI-driven attacks, cloud expansion, and the convergence …Download Whitepaper
Data Management in the Age of Cloud and AI
In today’s Asia Pacific business environment, organizations are leaning on hybrid multi-cloud infrastructures and advanced …Download Whitepaper
Middle-sidebar-banner
Case Studies

Bangladesh LGED modernizes communication while addressing data security concerns
To meet emerging data localization/privacy regulations, the government engineering agency deploys a secure, unified digital …Read more
What AI worries keeps members of the Association of Certified Fraud Examiners sleepless?
This case study examines how many anti-fraud professionals reported feeling underprepared to counter rising AI-driven …Read more
Meeting the business resilience challenges of digital transformation
Data proves to be key to driving secure and sustainable digital transformation in Southeast Asia.Read more
Upgrading biometric authentication system protects customers in the Philippines: UnionDigital Bank
An improved dual-liveness biometric framework can counter more deepfake threats, ensure compliance, and protect underbanked …Read more