Compare this to the recommended ‘breakout time’ limits and we get a gauge of the world’s current level of cyber-susceptibility.
Organizations from major industry verticals around the globe have been polled and found significantly under prepared to address breakout time—the critical window between when an intruder compromises the first machine and when they can move laterally to other systems on the network.
According to current recommendations, forward-leaning organizations should look to follow the 1:10:60 rule: One minute to detect threats, 10 minutes to investigate, and 60 minutes to contain and remediate an incident. A recent CrowdStrike report has unveiled some interesting results:
- Currently, 95% of respondents fall short of meeting the three timings of the 1-10-60 rule
- Only 11% of polled organizations can detect an intruder in under one minute; only 9% can investigate an incident in 10 minutes; and only 33% can contain an incident in 60 minutes. Only 5% claim to be able to achieve all three
- Intruder detection is the primary IT security focus for only 19% of respondents, despite 86% seeing one-minute detection as a cybersecurity “game-changer” for their organization
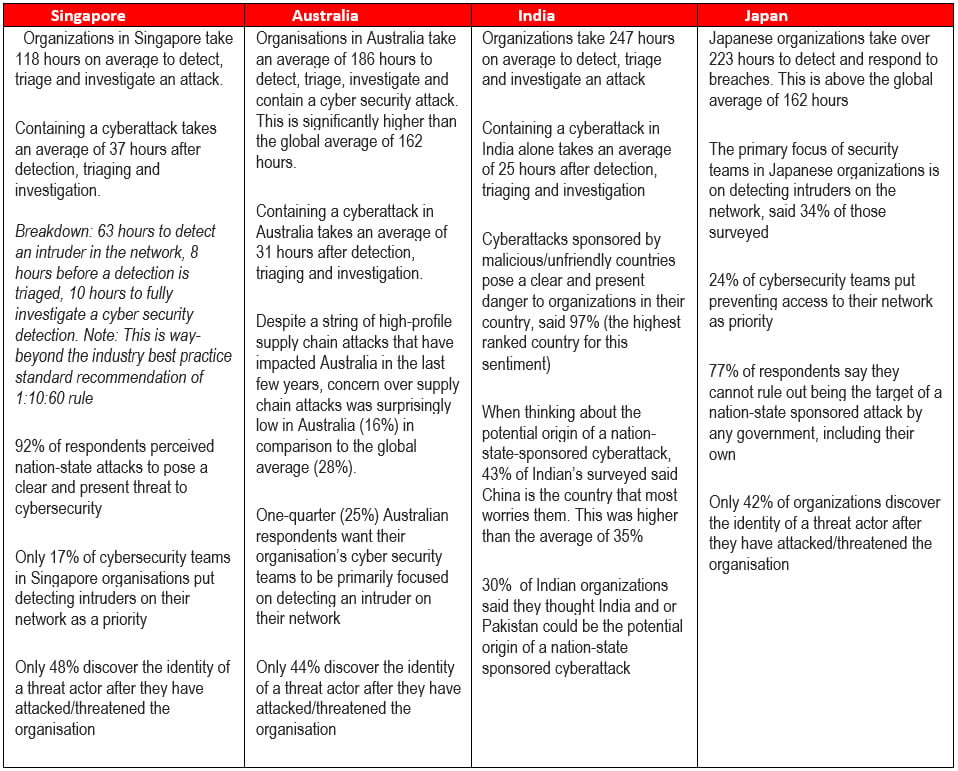
The 2019 CrowdStrike Global Security Attitude Survey, produced by independent research firm Vanson Bourne and commissioned by CrowdStrike, polled 1,900 senior IT decision-makers and IT security professionals in the U.S., Canada, U.K., Mexico, Middle East, Australia, Germany, Japan, France, India and Singapore across major industry sectors. The report details the attitudes and beliefs of those in charge of cybersecurity, and tracks how they are faring against sophisticated and pervasive cyber attacks.
The situation in our region
Seven days of round-the-clock panic
The survey finds that the process of detecting, triaging, investigating, and containing a cyber incident takes organizations globally on average nearly seven days of working around the clock (totaling 162 hours), with an average of 31 hours to contain a cybersecurity incident once it has been detected and investigated. As a result, the majority of respondents (80%) report that in the past 12 months, they have been unable to prevent intruders on their networks from accessing their targeted data, with 44% pointing to slow detection as the cause.
Organizations’ concerns about different types of attacks also differ across the report. Notably:
- The rise in the number of those who had experienced multiple supply chain attacks, including within the past year—doubled from 16 % to 34%. Yet, concerns surrounding supply chain attacks decreased on a global average from 33% in 2018 to 28% in 2019.
- In the same vein, the number of organizations paying ransoms to retrieve data encrypted in a software supply chain attack also more than doubled from 14% to 40%. The report indicates that over 50% of the food and beverage, hospitality, and entertainment and media industries have paid ransoms in the past 12 months in order to recover data encrypted in a software supply chain attack.
- An average of 83% of respondents believe that nation-state sponsored attacks pose a clear danger to organizations within their country, with India (97%), Singapore (92%) and the U.S. (84%) experiencing the most heightened sense of risk from nation-state threats.
According to the VP of CrowdStrike Services, Thomas Etheridge, “organizations are challenged to achieve the kind of speed required to match sophisticated nation-state and eCrime adversaries known to target governments and enterprises. There is still a significant reliance on legacy infrastructure that does not address security for today’s organizations from a holistic standpoint to stop breaches.”
Clearly, a reliance on legacy infrastructure, exacerbated by a lack of resources and expertise, has hampered organizations’ abilities to mount an effective defense against the adversaries they face. Etheridge feels that forward-leaning companies must embrace the cloud for endpoint security to give their teams comprehensive visibility and crowd-sourced protection to address effectively a full range of security and operational needs.
To improve their abilities to achieve this, businesses can employ a variety of solutions from increasing budgets, training and additional staff, to having a more comprehensive understanding of the attackers targeting their organizations, and taking a more proactive “threat hunting” approach to readiness.





















