Here is an update on the voluminous attack attempts barely a week from public disclosure of the Apache Log4Shell vulnerability.
Precisely one year after the infamous SolarWinds hack, and with organizations still struggling to protect the software supply chain from third-party risk, the Apache Log4j vulnerability exploit has caught security teams by surprise during a weekend.
Unlike other major cyberattacks that involve one or a limited number of software components, Log4j is basically embedded in every Java based product or web service, and vulnerabilities are very difficult to remediate manually.
Once an exploration was published, scans of the internet ensued (to allocate surfaces which are vulnerable due to this incident). Those who won’t implement a protection are probably already scanned by malicious actors.
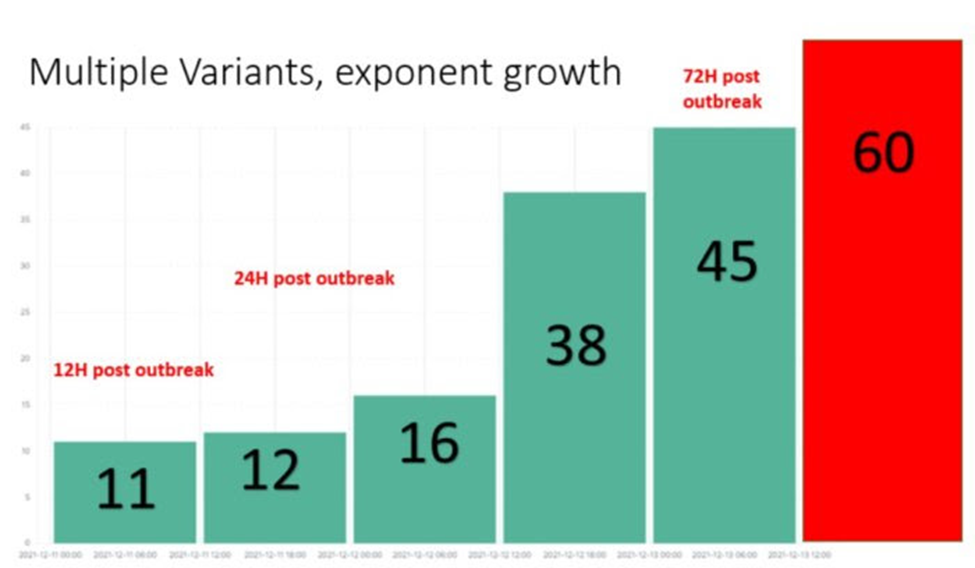
Since 9 December (Friday) when the vulnerability was first reported, actors around the world have been on the lookout for exploits. The number of combinations of how to exploit it has given attackers many alternatives to bypass newly introduced protections. This means that one layer of protection is not enough, and only multi-layered security posture can provide resilient protection.
Fast and furious attack numbers
Now, nearly a week after the disclosure, Check Point Research (CPR) has provided some interesting statistics:
- Early reports on 10 December showed merely thousands of attack attempts, rising to over 40,000 during Saturday, 11 December.
- In less than 24 hours, over 60 new variations of the original exploit were being introduced.
- 24 hours after the initial disclosure, CPR sensors recorded almost 200,000 attack attempts across the globe leveraging this vulnerability.
- As of 72 hours post initial disclosure, the number hit over 800,000 attacks.
- These numbers show clearly that Log4j is one of the most serious vulnerabilities to have been disclosed in recent years, and the potential for damage can be incalculable.
- Since then, CPR has prevented over 845,000 attempts to allocate the vulnerability, with over 46% of those attempts made by known malicious groups. Globally, over 40% of corporate networks have seen an attempted Log4j exploit.
- The spread per countries is overwhelming and crosses continent and regions, ranging to over 90 countries in all regions. The impact itself is also wide, with peaks reaching over 60% of corporate networks impacted, and many distributions seeing over 50% of corporate networks within the country beings impacted.
Brace for long haul Log4j
Because of the complexity in patching Log4j and the ease with which malicious actors can exploit the vulnerability, this ‘cyber pandemic’ is likely to stay globally for years to come, unless the world takes immediate action to prevent and mitigate attacks.
Given the upcoming holiday seasons globally—when security teams may be slower to implement protective measures—the threat is imminent.
This highly contagious threat spreads rapidly and has multiple variants, which facilitate many more ways of inflicting harm. CPR has set up a dedicated website to provide actionable resources that readers can use to pursue their own proactive defense strategies. Other resources are also available from the Cybersecurity & Infrastructure Security Agency CISA and individual cybersecurity solutions providers.