Even as the novelty of pandemic threats ease in 2021, cybercrooks continue their assault on remote workers not well-trained for cyber-vigilance.
The rise of ransomware, double-extortion ransomware and Ransomware-as-a-Service has been well documented throughout 2020.
Recent high-profile cases such as the DearCry ransomware attack on unpatched Microsoft Exchange servers just go to demonstrate how cybercriminals are wasting no time in exploiting vulnerable organizations.
According to a ransomware threat report by Unit 42 of Palo Alto Networks, 2021 brings more challenges ahead:
- Cybercriminals made and demanded more money than ever in 2020
• The average ransom payment nearly tripled from US$115,123 in 2019 to US$312,493 in 2020.
• The highest ransom payment doubled from US$5 million in 2019 to US$10 million.
• The highest ransom demanded doubled from US$15 million in 2019 to US$30 million in 2020. - Rise of ‘double extortion’ where hackers lock and steal data and Ransomware-as-a-Service (RaaS)
• There were at least 16 different ransomware variants exploiting victims by encrypting and stealing/threatening to expose data on top of the main ransomware threats.
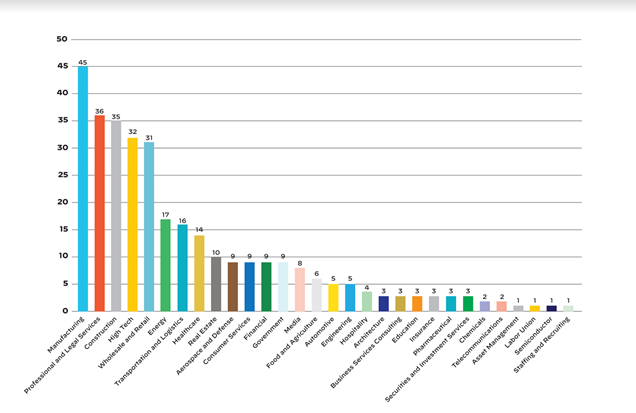
The information in this report was derived from analyses of available threat data for the 2020 calendar year and a look back to 2015–2019 where relevant. Unit 42 researchers analyzed ransomware leak site data available on the dark web and public websites, global threat data available via internal and external sources, and the firm’s breach response data for the US, Canada, and Europe.
The report concluded that, since initial access is relatively consistent across all ransomware variants, organizations should maintain user awareness and training for email security as well as consider ways to identify and remediate malicious email as soon as it enters an employee’s mailbox.
Organizations should also ensure they conduct proper patch management and review which services may be exposed to the internet. Remote desktop services should be correctly configured and secured, using the principle of least privilege wherever possible, with a policy in place to detect patterns associated with brute-force attacks.