A new study shows how implementing strong defence-in-depth protocols and up-to-date offline backups can mitigate any ransomware attack quickly.
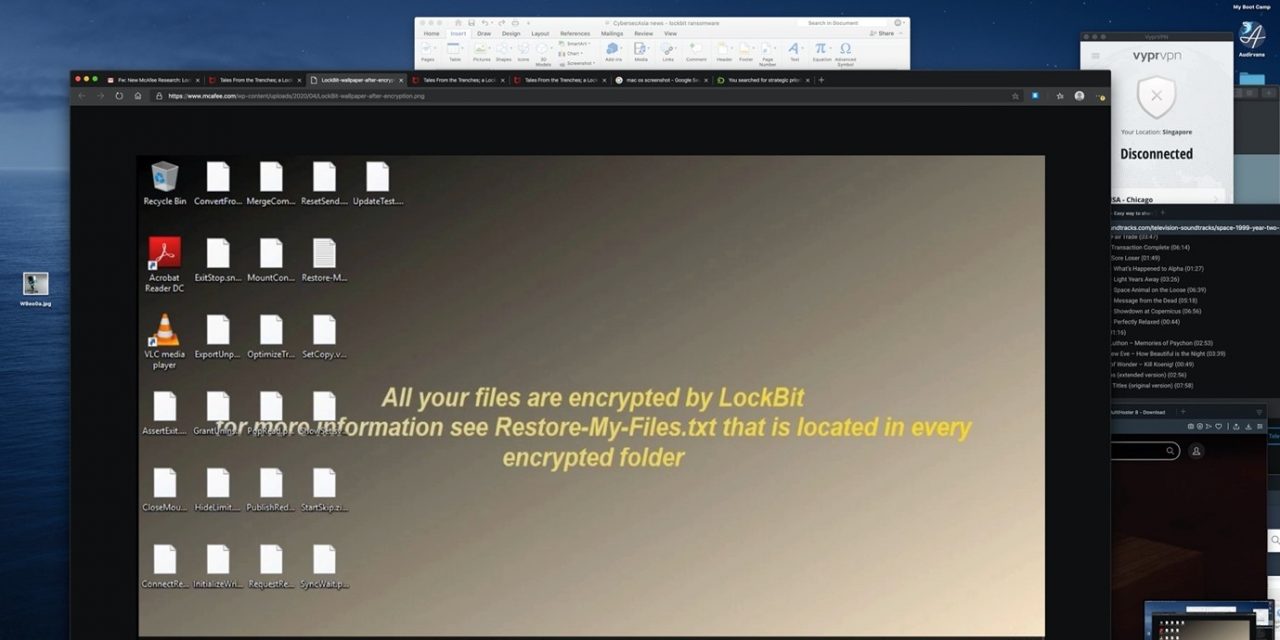
In recent months, a ransomware family of malicious code called LockBit has gained heavy momentum and captured the attention of many in the cybersecurity community since its emergence.
New research, which combines insights from McAfee’s Advanced Threat Research team and Northwave incident response, has provided a first-hand look into the unique characteristics of LockBit based on a real-life attack on a Dutch logistics company, as well as its unique operations.
As a toolkit, LockBit is only offered to a select group of cybercriminals, likely signifying that the creators are gearing up for larger operations. The group behind LockBit put a deposit of US$75,000 (10.5 BTC) in the underground escrow to show other criminals they mean business—something other major ransomware families (like Sodinokibi) did in their initial stages.
The research involved detailed observations of the attack from initial access, to lateral movement, ransomware deployment and unique aspects of the ransomware such as additional automation and changes in new versions.
It was discerned that a new trend is gaining traction in cyberattacks: targeted ransomware.
McAfee researchers see this being executed in two stages:
- Attackers steal info to gauge the worthiness of the target;
- Attackers then launch the attack on worthy targets, using the collected sensitive data and knowledge on how much an organization could pay to get their data back.
Another way LockBit works is through the use of Jabber-bot chatbot to communicate with victims and perform essential functions in that time, which ultimately led the victim to pay the ransomware.
In the real-life case featured in the research, there were no recent offline backups. So, with the backup servers (including the backups) encrypted as well, and a complete rebuild not being an option, there was no way for a successful and swift recovery other than by paying the ransom.
Both McAfee and Northwave concur on the perspective that ransoms should not be paid. Paying does not only support the criminal business model but also finances other forms of crime, such as the online drug trade.